Introduction
Welcome to your friendly guide to data security & compliance. This guide aims to help market researchers tackle the security issues that impact their roles.
We know the topic can be a bit dry, so we put the essential information in an accessible, user-friendly format.
Disclaimer
This guide provides useful information for Market Researchers who are invested in the security of the data they collect. However, this guide does not offer legal or compliance advice. You should seek professional support and advice where needed.
Additionally, while the information contained in this document was correct at the time of writing, regulations and best practice recommendations do change.
Are you ready? Let’s get started.
Why you should care about data security & compliance
The fact that you’re reading this guide indicates that you already recognize the importance of data security, so we won’t dwell too much on this point.
When it comes to data security & compliance, there are legal requirements that businesses must adhere to.
Additionally, the reputation of the research industry as a whole is also at stake. Researchers need participants. Therefore, we must do everything possible to protect the researcher-participant relationship by keeping their information safe.
Research participants open up and share their thoughts, feelings, as well as personal information to help generate insights that are used to guide decision-making. The reason they share that information is because they trust the researchers. Without trust, Market Research becomes a whole lot more challenging.
Data security considerations for researchers
Why is it important?
Market Researchers handle a myriad of information and different types of data. Some of the data types you’ll likely come into contact with are:
1
Sensitive
Within the broad category of personal data, some information is particularly sensitive. Due to the nature of research, this is also information that may often be collected. Examples include race, ethnicity, sexual orientation, health data, as well as religious beliefs and political opinions. Whether you find yourself dealing with one, or all of these data types, you will want to prevent it from falling into the wrong hands.
2
Personally Identifiable Information (PII)
This is information that could potentially identify a specific individual. Some information, such as full name or passport number, is enough to identify an individual on its own. In other cases, the combination of separate pieces of data may make it possible to identify someone at an individual level.
3
Confidential
Market Research provides unique insight which helps organizations make decisions. In light of this, often the themes and topics that form the research involve confidential information. Examples include; focus groups on innovative solutions, feedback on prototypes and testing of potential marketing messages.
Participant-led consideration
Specific groups
As well as the general considerations you need to apply to all participants, there are additional restrictions for particular groups, such as children.
Oftentimes, classifications make their data particularly sensitive. There can be other specific research guidelines in place to ensure researchers approach and interact appropriately with these individuals.
Location
When conducting research in different countries, there are elements such as language, culture and time zones that can all pose unique challenges. In addition, different locations can often have different rules and regulations in place. It is often not as simple as applying the rules you would in one country to participants elsewhere in the world.
Make sure you know of any location–specific data protection and privacy laws that you need to adhere to.
Project design & methodology
In the design phases of a research project, you should have a clear idea of who the participants will be and what you’ll be researching. This preparation will help you plan for the type of data you will collect. You’ll be able to determine whether it includes personal information that’s particularly sensitive and confidential. What is more challenging to know is how participants will respond and what they will say.
Along with identifying the type of data you’re requesting, you should also consider data you might unintentionally collect. For instance, respondents might mention personal or sensitive details in open-ended questions or comments.
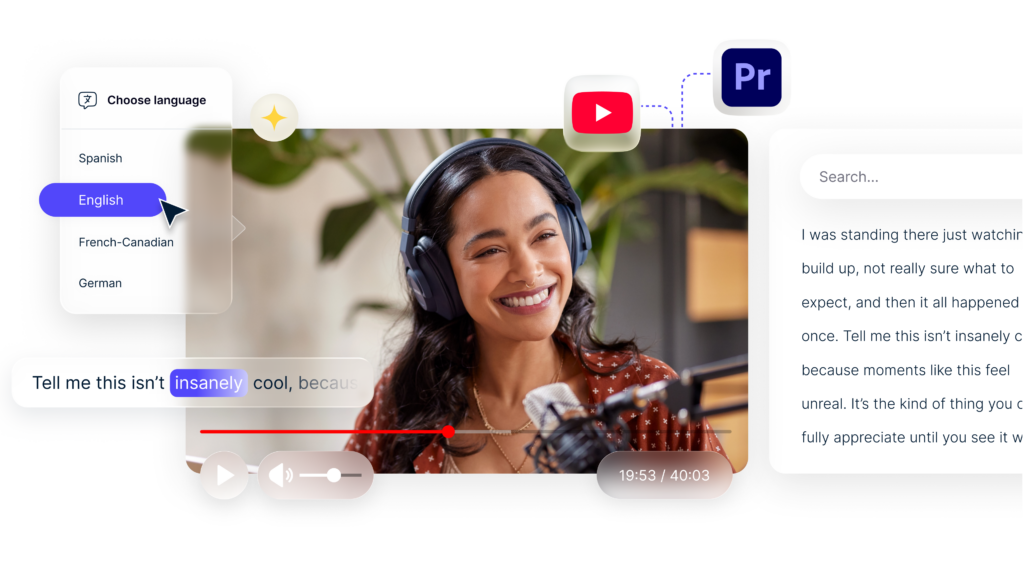
Video & Audio
The use of video rapidly accelerated during the pandemic as people looked for new ways to conduct research. Video became a solution for recording data from interviews that previously happened face-to-face.
Regardless of what the respondents might talk about, recordings of their voices and faces could qualify as personal data.
Operational information
In addition to the information that you need for your research, you’ll inevitably require other unrelated information from your participants. This may include, but is not limited to:
- Name & contact details
- Bank details or address for an incentive payment IP address for deduplication of survey responses
Much of this data is outside the scope of the project deliverables. However, it’s also essential and needs your careful consideration. You’ll be responsible for protecting all of the information you collect, transfer and store. You may only need this type of data in the short term.
Still, you must consider all of the data that forms you collect for the project, not just the information you explicitly ask for.
Best Practice
Although the specific requirements and standards for data security vary case-by-case, a good rule of thumb is to always err on the side of caution. Keeping things consistent and being diligent will avoid situations where you inadvertently put information at risk.
Here are some basic principles that will help you establish data collection, handling and storage best practices:
- Only collect the data you need
- Only give access to people who need it
- Delete data after a set time period
- Be clear and transparent about your data practices
- Have people opt-in and actively agree to data collection rather than opt-out
Only collect and keep the data you need
When running projects, it can be tempting to ask for as much information as possible. You never know what insights it might reveal, right?
It’s best to only collect the information you need. Limited data collection is particularly important when it comes to personal or sensitive data. This practice makes for a better user experience as well.
Only give access to people who need it
Despite the trustworthiness of your colleagues, accidents do happen.
You can minimize the risk of human error by reducing the number of people who have access to your data.
Technology can be your friend in these cases. The right tools can help you lock down access, ring-fence data and prevent hackers as well as human errors.
Deleting data after a certain amount of time
I think we can all be guilty of the ‘just in case’ mentality when it comes to information. Just a quick glance into most people’s email boxes or computer drives will attest to that. It’s good to review what information needs you need to keep and for how long. You may also find that you can remove some personal data while keeping other results intact. Taking these steps can help minimize any risks.
Be clear, open & transparent
If you go through the stages above it’s easy to be clear, open and transparent with your participants. Transparency gives people the information they need to ensure that they can make an informed decision about taking part in any research. With this clarity, they know where their data will go, what you’re using it for, and how long you’ll be keeping it. Participants should also know they can ask you to remove their data in the future.
Opt-in, not opt-out
Some opt-ins leave you so confused about whether you’ve actually opted in or out. This format isn’t great from a user perspective.
No one likes to feel that they’re being tricked into something.
Make any opt-in messages super-clear; at least then, you’ll know that participants really want to be involved.
How to reduce the risk of a data breach
Here are a few steps you can take to reduce the chances of a data breach:
1. Conduct an audit
A good first step is to conduct an audit to understand what data you have already, as well as information you’re likely to collect in the future. Your organization might’ve already conducted this type of audit as part of a government requirement like the GDPR, but it’s good practice to revisit periodically.
Anyone working on a project should have a good understanding of:
- The type of information you’re collecting
- How to collect, manage and store the data
- Who has access to the data
- How long to keep the data
- Who is responsible for deleting data when required
Processes, policies & training
Processes and procedures may have many of us rolling our eyes, but they are essential for ensuring compliance.
Careful processes provide structure and workflows to minimize any risk and provide a framework to deal with any breaches quickly and efficiently.
All too often, though, people put policies and procedures in place but don’t offer the necessary training to accompany them. Alternatively, teams might not adhere to them as rigidly as they should.
For example, maybe a client emails over a list containing some personal details rather than using the secure channels that you put in place, but you let it go, just this time. Those seemingly small issues can lead to big problems, and we’ll be discussing human error in more detail shortly.
You want to establish a culture where data security is part of the everyday language. From the initial induction process all the way through to when someone leaves the organization, there should be an understanding of security requirements and best practices. You also want people to feel comfortable raising any concerns and reporting any issues that you’ll want to investigate.
Using technology
Technology can be a great support when it comes to security and compliance, but it also needs processes in place to ensure we’re benefitting from the capabilities on offer.
This can include making sure we install the latest updates to counteract new security threats, using secure portals and encryption for data transfer and storage, and accessing information through secure means such as virtual private networks (VPN).
Also, remember the importance of strong passwords and enabling two-factor authentication (2FA).
More on technology later.
Keeping your data safe
According to CybSafe, human error caused a whopping 95% of cyber data breaches in 2022¹.
Minimizing human error
Although, as we’ve mentioned, technology can play a useful role in data protection, it can’t eliminate all risks. As individuals, we need to stay vigilant to threats. Even when we’re using all the technology available to us correctly, there is still a chance of human error. That risk is potentially even greater if we become complacent because we expect technology to do the work for us.
For instance, you’ve probably received a phishing email in the past.
Some are more obvious than others. Most of us are likely on to the Nigerian prince scam. However, other more convincing attempts to get sensitive information or money could appear in your inbox. They may look like they come from your bank or another service you use.
Phishing emails can also target businesses. These messages may look like they’ve come from someone in your organization. Not only do the emails look realistic, but they may also use the style and tone you’d expect.
When it comes to thwarting these attacks, good policies play a critical role. By setting out clear processes for sharing sensitive and confidential information, you can mitigate the impact of a phishing incident. If in doubt, pick up the phone or use another type of communication to double-check. When it comes to suspicious messages, you’re ‘better safe than sorry.’
Here are some other examples of human error to watch out for:
- Accidentally downloading a malware-infected attachment
- Sending data via insecure means such as email
- Accidentally sending information to the wrong person (recall, recall!)
- Revealing information through social engineering
- Leaving sensitive or confidential information unattended in a non-secure environment (that quick stop for a coffee or leaving a bag on a train)
And everyone’s favorite – Passwords!
- Weak passwords (i.e., 123456, password)
- Reusing passwords
- Writing down passwords
You get the point. Passwords can be a problem. It’s vital to consider ways to reduce the risks associated with passwords. For instance, develop a well-devised password policy or implement a password manager.
How technology can help
With the influx of flexible working environments, locations and hours, we should consider some security-related aspects of working from home.
Many of these also apply when we’re on the move and making use of the connected world.
When we’re tucked up in our offices, there are layers of security to protect our servers, networks and individual machines.
As the lines become increasingly blurred, it’s easy to pick up a personal device to carry out work tasks or jump on a public WIFI network to send a quick email.
However, in doing so, we are increasing the risk of a data breach.
Layers of security, when accompanied by the right processes and training, can help to mitigate the risk and ensure you feel confident in what you should and shouldn’t do. Here are just some areas to be aware of when dealing with data.
Encryption
Encryption only allows those with the decryption key to decipher the information. Encryption is common across the Internet.
Also, when you use an HTTPS site with a reassuring padlock, it the connection is secure, and the identity of the server is trusted. Checking for this is another way to protect data online.
You should stick to using encrypted and secure methods of transferring data as well as storing it.
Virtual Private Networks (VPN)
You may already be using a VPN. Many companies provide these. You can also sign up for a VPN for personal use.
A VPN provides a secure connection between you and the Internet. This extra protection can be particularly beneficial if you find yourself using public WIFI. VPNs have other uses, some of which aren’t exactly legal. Make sure you’re using them for the right reasons.
Two-factor authentication
Many sites and services will offer you a 2-factor authentication option (2FA) in which you need two ‘factors’ to gain access. There are three general categories of factors for authentication: what you know (a password), what you have (your phone), what you are (your fingerprints)
Typically, you must provide a known piece of information, such as a password, along with another method. The second method could be something like an authenticator app on your phone or a unique characteristic, like a biometric identifier (fingerprints, facial or voice recognition).
Keeping up to date with updates
If you’re like us, your heart sinks a little every time you get the ‘an update is available’ message on a device. The update itself isn’t really the problem, but it always seems to pop up at an inconvenient time. Also, they don’t give you any reliable indication of how long it might take. You might lose the ability to use the device for anywhere from a few seconds to hours!
Despite the irritation, the updates are extremely important. They may include new or enhanced features, but the key reason to apply them in a timely fashion, is that they often contain security fixes.
When vulnerabilities are detected, ‘patches’ are delivered through updates to resolve the issues and keep your data safe.
So, next time you start to hover over the ‘remind me later’ option, maybe think twice.
2FA provides an additional layer of security, but it’s often optional rather than mandatory. Unfortunately, it can put some people off as it’s an extra step in the process. However, it is usually quick and easy to set up.
Pseudonymization and anonymization
Pseudonymization is a security technique that protects data subjects. This process makes it impossible to identify a person without the means to reverse the pseudonymization. You’ll likely have seen this in action on a research project where the researchers replace personal data such as names with an ID or reference number. Although it helps protect identities, this process doesn’t change the nature of the data. The information will still fall within the scope of regulations such as the GDPR.
Anonymous data, on the other hand, is not personal data at all, and so is outside the scope of GDPR, which has huge compliance benefits. Anonymized data does not relate to an identified or identifiable person and therefore poses no risk to individuals. It makes sense to anonymize data wherever you can; however, make sure you’re clear that the information is truly anonymous and not just using pseudonymization.
GDPR
What is GDPR?
It’s been around for a while, but let’s do a quick recap.
The General Data Protection Regulation (EU) 2016/679 is an EU regulation the took effect on 25 May 2018.
It applies directly in all EEA countries and addresses the processing of personal data. At the heart of the GDPR are six key data protection principles, together with the concept of accountability and expanded rights for data subjects.
Why is it important?
Personal data goes one step beyond PII and looks at data relating to identifiable individuals, which is quite a broad scope. Of course, personal data isn’t the only thing you need to consider when you’re thinking about information security, but the statutory obligations placed on organizations by the GDPR mean that it’s likely to be one of your biggest compliance burdens. Additionally, the penalties for getting it wrong can be steep –  ask Google (fined €50m), British Airways (fined €22m) and H&M (fined €35m) Companies like Amazon and Meta could be facing even larger fines.
Many of the best practices we’ve talked about throughout this guide (like only collecting data that you need for your purpose, for example) become legal requirements under the GDPR when you’re dealing with personal data. It’s important to make sure that you have a good understanding of your obligations as well as the right processes and procedures to meet those obligations.
Implications for Market Research
The implications of GDPR on research (and for many areas of business) are wide and far-reaching. It impacts how you connect with participants, what information you can hold about them and what details you need to provide them in return. It also gives participants greater control over how researchers use and delete their information.
GDPR provides some interesting challenges for market research in particular, such as when a client or brand wants to remain anonymous. Whether you are a fan or not, it does provide greater transparency for individuals and instills best practices in (most) businesses.
Trust is an important factor in engaging participants, and GDPR helps to nurture this.
It’s a really good idea to be clear, open and transparent when you’re dealing with data. This practice aligns well with the first data protection principle in the GDPR, which says that personal data must be processed “lawfully, fairly and in a transparent manner.” If you set out to embed that principle in your organization’s culture, you should find that compliance with the other data protection principles and the GDPR isn’t really a challenge.
Brexit Implications
For European research
GDPR remains in place for the European Union. When you conduct research across those countries, you need to abide by the regulations.
you’re part of a UK organization that doesn’t have an EU establishment, you’ll also need to consider whether you need a GDPR EU representative in relation to any processing that falls under EU GDPR.
For UK research
The UK has been subject to GDPR, which means businesses have policies, processes and procedures in place to protect data and privacy in line with the regulation. Even though the UK left the EU, there is now a UK version of the GDPR in domestic law. This, together with the Data Protection Act 2018, forms the backbone of the UK’s data protection regime. These laws also apply for foreign companies operating in the UK. For instance, US companies that aren’t established in the UK may need to appoint a UK GDPR representative.
Currently, at least, the UK GDPR and the EU GDPR remain closely aligned. However, over time it’s inevitable that there will be some divergence on both sides. You’ll want to track any changes if your organization processes data in both the UK and EU.
International transfers
Whichever version of the GDPR you’re working with, it’s important to be aware of the restrictions in place concerning international transfers. Today, this is particularly important thanks to the wonderful world of cloud services and increases in remote working arrangements.
The default position in the GDPR is that international transfers should only occur where the receiving country provides an adequate level of data protection. This basic principle aims to offer data subjects equivalent rights (and also ensure that they’re enforceable).
If the country you’re transferring to is not considered adequate, then you’ll need to put in place what the GDPR calls “appropriate safeguards.”
The GDPR outlines several possible approaches to this, but according to the current guidance, box-ticking is not enough. The transferring party has a duty to ensure that whatever safeguards they put in place are effective.
Which countries are adequate? So far, only a relatively small number of countries made the cut. The United States, for example, is currently not considered to be adequate for the purposes of the GDPR. This, of course, can have important implications for US companies and any business working with 3rd party vendors.
Working with 3rd parties (including transcription providers)
It’s not uncommon for researchers to use third parties for a variety of purposes.
This includes third-party software such as text analytics, Automatic Speech Recognition (ASR) and survey platforms. As well as using other services such as human-based transcription.
If you’re at an agency, you’re the one who has the contract with the client, or if you work at a brand, it’s you the participants have put their trust in.
So, either way, it would be devastating if all your hard work to make sure your practices are secure falls apart because of a vendor.
This isn’t to say third-party suppliers aren’t secure. They certainly can be. However, it’s your responsibility to do your due diligence on the suppliers you select. It’s also good to remember that for GDPR compliance, any processing vendors perform on behalf of the data controller must be governed by a written contract.
Here are some of the important aspects to consider. You might already be aware of some of these, but others may give you a new perspective.
Who has access to your information?
Is your data locked down as much as possible, or do many, potentially 1000’s of people, have the ability to access any information and content you provide? As we mentioned, human error is a big problem. Minimizing access to data is usually a good idea.
Where are the people who have access to your information based? It can be challenging to pursue any security violations when people are in different locations, even if a Non-Disclosure Agreement (NDA) is in place.
In the case of Verbit, we provide secure portals where you upload your content. We also provide access to the content to those directly involved in the project (typically the transcriber & account manager).
Transcribers carry out the transcription within a secure environment. They can’t download the files to their computers. Once your transcript is completed and quality checked, you retrieve it via a secure portal.
HTTPS websites & portals where you are sharing information
HTTPS is a secure version of the transfer protocol which is used to send data between a web browser and a website. This process means that data transfers are more secure because the data is encrypted. On an HTTP site, the data transfer isn’t encrypted. As a result, anyone who intercepts the data can read it.
Whenever you enter any details into a site, be sure to check that the site is HTTPS rather than just HTTP. Checking this isn’t just a good practice to follow for work. It’s also smart for personal browsing.
There are a few ways you can check for this:
- View the full URL and check that it starts with ‘https://’
- Look for the padlock in the browser address bar
- Ensure you do not see any ‘this website is not secure’ messages
Think of this as the first line of defense. However, there are additional signals of a secure service that you should also look for.
What processes are in place?
We’ve talked about the importance of processes and procedures to minimize risk. The same applies to any third parties that have access to your data. Here are some concerns and questions about third-party vendor security.
Are their servers locked down as much as possible to restrict access?
Security-conscious companies will require authentication to access data and may also limit access to specific IP addresses.
Is it possible to download your content to a non-secure environment or make copies for external storage?
Ideally, your data should stay within secure, encrypted environments at all times.
Is the third party relying on Data chunking?
Data chunking splits your data into chunks, so if a breach occurs, the bad actor would only have a small piece of the puzzle.
Although it creates a challenge, it’s not a guarantee. Your data is still a risk without the addition of other, more stringent measures.
What indications are there that a supplier takes data security seriously?
They shout about it
Well, they don’t have to literally shout, but they may raise their voice slightly or use a bold font! If companies have invested in security, they will have this information readily available for you, usually on their website. If you can’t find what you’re looking for, get in touch, as it should be easy for them to provide you with their security credentials.
ISO certifications
If you’ve ever been through an ISO certification, you’ll know they are pretty extensive and intensive! Companies will have dedicated resources to not only achieving their certifications but in their ongoing management of the associated processes and systems too. It provides a rubber stamp from an impartial third party that they meet the required standards.
The certification to look out for is ISO 27001. ISO
27001 relates to all aspects needed for a robust information security management system (ISMS).
It’s also worth checking what aspects of a business the ISO certification covers. It’s not uncommon to find that an organization has an ISO 27001 certification covering only a limited scope of their ISMS, their data center, for example. This limited scope may leave large gaps in their information security.
ISO 27001 is an internationally recognized credential that many consider the gold standard for ISMS, covering all forms of information, including digital.
Another way to check a third-party vendor’s security is to look at a SOC 2 report. This document details the security and risk management practices of vendors. Specifically, SOC 2 relates to Software as a Service (SAAS) providers and any business that stores data in a cloud.
Willingness to sign non-disclosure agreements (NDAs)
Even when a company has put in a vast array of security measures to minimize risk, it’s impossible to eliminate it altogether.
Your company may require that any third parties sign an NDA to assign greater legal accountability for any data. This precaution can provide an additional layer of reassurance and also act as a warning sign if a company refuses.
Remember, though, when parties operate in different countries, it can be difficult to effectively pursue claims, so don’t rely solely on an NDA.
Helpful Resources
We’ve aimed to touch on the core data security and compliance elements that you should be aware of in the Market Research field. Here are some additional resources you might find useful that explore these topics in more detail.
ISO – https://www.iso.org/home.html
MRS – https://www.mrs.org.uk/
ESOMAR – https://www.esomar.org/what-we-do/code- guidelines/esomar-data-protection-checklist https://www.esomar.org/uploads/public/knowledge-and- standards/codes-and-guidelines/ESOMAR_Briefing-Questions- When-Considering-Tools-and-Services-for-Unstructured- Data.pdf
Sources
1 – CybSafe analysis from the UK Information Commissioner’s Office (ICO)
You made it! Thanks again for choosing this guide.
We hope it’s helped you to feel more confident about data security and compliance.
If you have any questions about data security or our transcription services, we’d love to hear from you.
You can get in touch with Verbit!
Stay safe out there!